Freedom Mobile customers could be at risk of malicious hackers gaining details such as their address, phone number and full call history, an anonymous hacker on the carrier’s subreddit has reported.
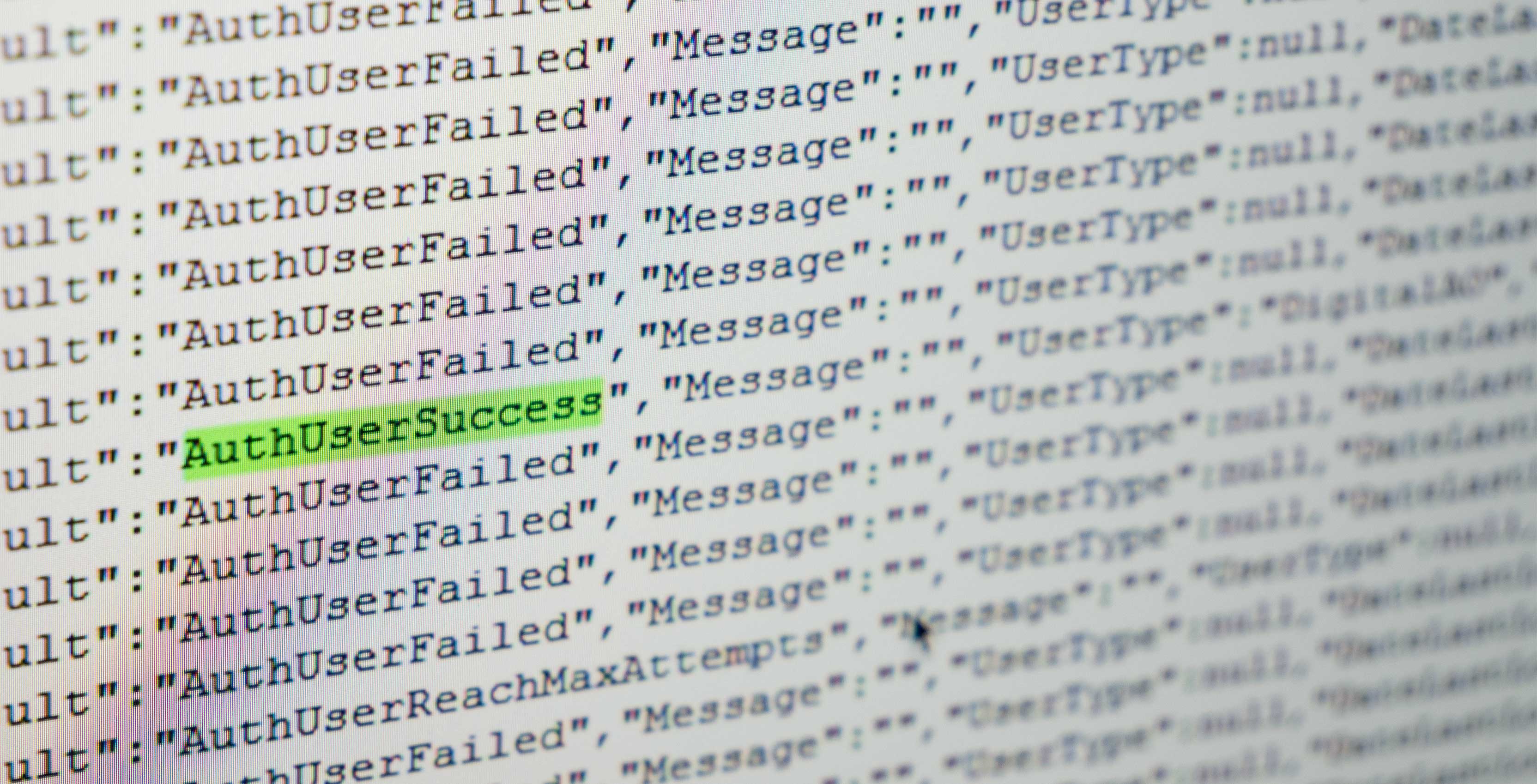
The hacker, who goes by the username NullHumanity, submitted their claim on the Freedom subreddit on Sunday evening, providing a screenshot of code that appears to show them successfully brute forcing user logins.
Brute force
In an email discussion with MobileSyrup, the hacker said that Freedom Mobile’s customer login system is “forced to the Phone Number/PIN model,” and that customers can’t change this even by calling support, making it easy to brute force logins.
This is because there are only 10,000 possible combinations for PINs (many of which are easy to guess due to their popularity, i.e. ‘1234’) and phone numbers are fairly easy to access.
“There are lots of services out there to identify carrier numbers,” NullHumanity wrote in the Reddit post.
The hacker said they have currently identified 2,000 at-risk accounts on Freedom Mobile’s MyAccount page, but do not intend to do anything malicious with the information they have gained. They believe it would be possible to target as many as 350,000 accounts based on their program’s failure rates and Freedom’s current subscriber numbers.
NullHumanity reported that the following data would be available if a hacker accessed a secondary API using the phone number and PIN combo: full name, date of birth, address, email, phone number, full call history and billing history.
“A phone number is predictable and a 4 digit PIN isn’t secure. Figuring out matching sets can be automated easily,” says NullHumanity.
Are PINs strong enough?
For its part, Freedom Mobile’s vice-president of external affairs, Chethan Lakshman, stated over email: “The security measures we have in place cannot protect against guessing common passwords. We continue to strongly encourage our customers to use unique PIN numbers that are not easy to guess, and to change their PINs frequently to best protect their personal account information.”
Lakshman also said that Freedom continuously reviews its security practices and is “committed to making improvements and changes as appropriate to continue keeping our customers’ information secure.”
Freedom’s security measures, said Lakshman, are designed to protect Freedom Mobile customers’ information from malicious activity while “meeting customer demands for a resonable login process.”
NullHumanity reports the process for accessing customer information is overly simple, however.
“I wrote a script of 23 lines of code. Anyone with basic knowledge can do it,” they wrote, adding that they would not share details of their process due to the potential of making more customers vulnerable.
Stosh Fabricius, a software engineer at digital payments platform Toronto company Pungle, offered context on how it relates to other industries that use similar four-digit solutions, like banking.
“The four-digit PIN is generally combined with something. In banking, when I do the four digit number I also have my card. Only I have my card, and I know my PIN. But phone numbers are easily available,” said Fabricius.
“Their flaw is that phone numbers are widely known and given that I know half of the log-in credential, brute forcing a four-digit PIN is not difficult.”
Password versus PIN
NullHumanity said they first brought the issue to the attention of Freedom Mobile on January 30th, but that they were rebuffed by a series of representatives from Shaw’s legal department.
One contact reportedly told them that four-digit PIN numbers provide adequate security, citing broad use in the banking industry.
Subsequently, NullHumanity reported their findings to the Office of the Privacy Commissioner of Canada (OPC) on February 5th.
A representative from the OPC told MobileSyrup via email the issue is currently “not something we are aware of,” adding that it has no information to provide.
According to NullHumanity, the same method used for hacking Freedom’s system doesn’t work for Rogers, Bell (which recently experienced its own cybersecurity breach), Telus, Fido, Koodo and Virgin, all of which they checked after finding the vulnerability.
“There is a risk that exists, but it is so heavily mitigated by the password system in comparison to the PIN system. Their […] systems however are more comparable to major providers such as Facebook and Google.”
MobileSyrup has reached out to the major Canadian carriers for comment on their security measures.
In the meantime, the hacker says those who are concerned about the vulnerability should create as unique a PIN as possible.
Correction: Article updated to clarify that NullHumanity stated they did not access any information beyond phone number and corresponding PIN.
Via: Reddit
Image credit: Jarmoluk via Pixabay
MobileSyrup may earn a commission from purchases made via our links, which helps fund the journalism we provide free on our website. These links do not influence our editorial content. Support us here.


