While the exploit has already been patched, the first version of Fortnite’s Android installer featured a vulnerability that could have potentially allowed bad actors to install malware on devices.
The exploit utilized a method called a man-in-the-disk attack in order to take advantage of the way Epic handles instaling the game on Android devices, intercepting the request and loading malware in the process. In order for this to work, players would first need to install an app designed to seek out the specific flaw, says Google.
While normally this might be difficult to make happen, given Fortnite’s relatively young player base, as well as the prevalence of apps offering free in-game currency, it’s actually very possible that some players could have an app on their phone that meets these criteria.
Unlike most Android games, in order to install Fortnite, players first need to download the game’s installer, which then downloads the full version of the game directly from Epic. The request to download the actual game is apparently the portion of the installation process that is susceptible to hacking, says Google.
“It was irresponsible of Google to publicly disclose the technical details of the flaw so quickly”
Epic says that a fix for the exploit was released within the first 48 hours of Fortnite’s release, according to Android Central. Given that relatively short time period, it’s unlikely any bad actors took advantage of the exploit, though it’s impossible to know for certain. Still, this is a stark reminder of why mobile app stores like the Google Play Store can be a good thing in some situations, especially when it comes to security.
As expected, Epic isn’t exactly pleased with how Google handled the security hole. The developer says that Google is being “irresponsible” for publically releasing the flaw before most players had the chance to update the installer, according to a statement from Epic’s CEO, Tim Sweeney. Sweeney also says that Google “refused” to wait until more players have updated the game. Google’s security team first shared the vulnerability’s existence privately with Epic on August 15th.
“Epic genuinely appreciated Google’s effort to perform an in-depth security audit of Fortnite immediately following our release on Android, and share the results with Epic so we could speedily issue an update to fix the flaw they discovered. However, it was irresponsible of Google to publicly disclose the technical details of the flaw so quickly, while many installations had not yet been updated and were still vulnerable,” said Sweeney in a statement.
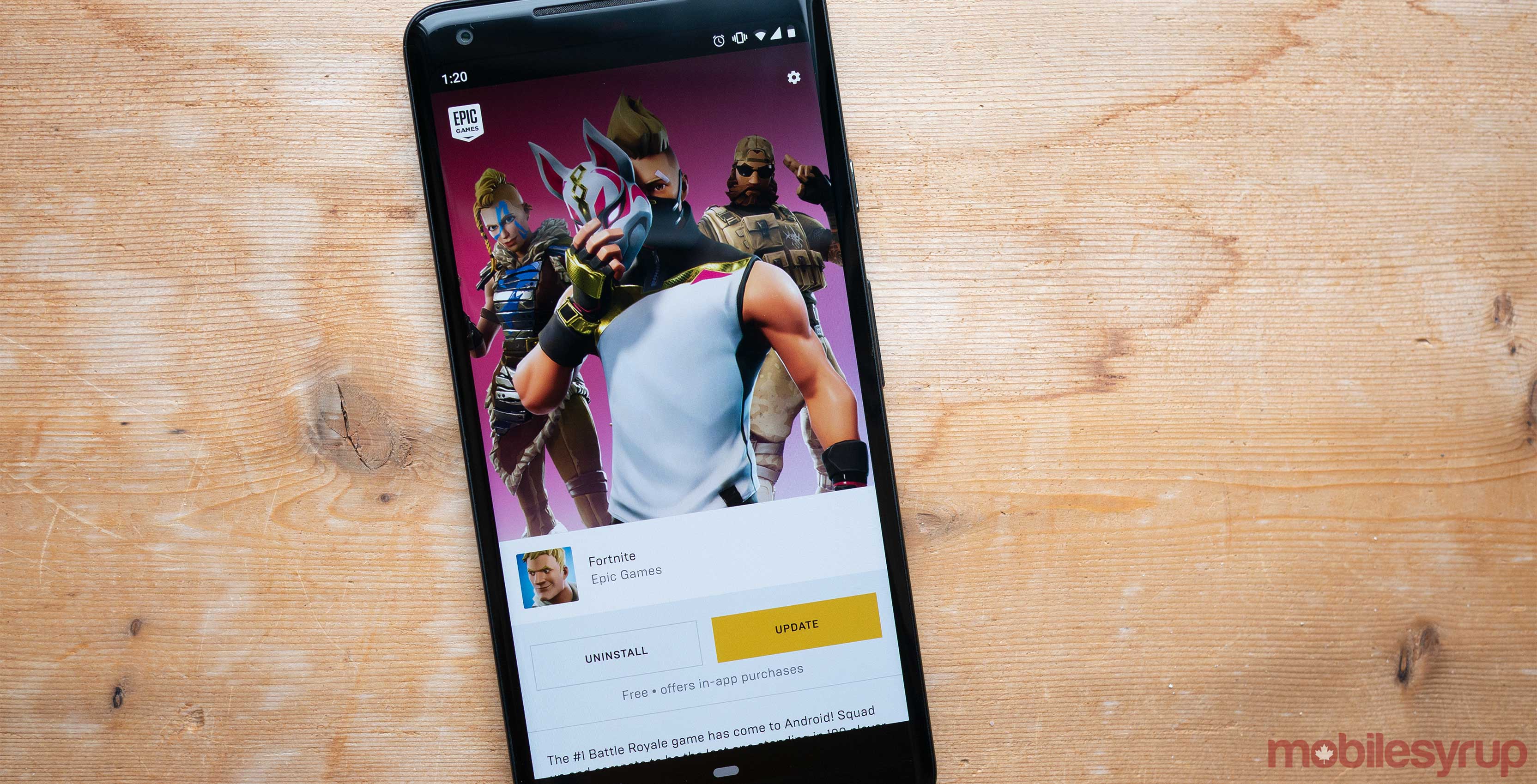
The Fortnite installer that features the fix is version 2.1.0. In order to check what Fortnite installer you’re using, navigate over to the app’s settings.
It’s likely the fact that Epic opted to circumvent the Play Store with the release of Fortnite, played some role in how Google handled the overall situation.
Source: Google Via: Android Central
MobileSyrup may earn a commission from purchases made via our links, which helps fund the journalism we provide free on our website. These links do not influence our editorial content. Support us here.


