By now, you’ve heard of Heartbleed. You’ve heard that this bug can be exploited to allow hackers to gain sensitive information from well-known services, many of which are still in the process of being patched. Just this morning, after days of outages, the Canadian Revenue Agency said that it has been subject to data theft from Heartbleed, likely between the time the bug was made public and the time the government decided to shut down its databases.
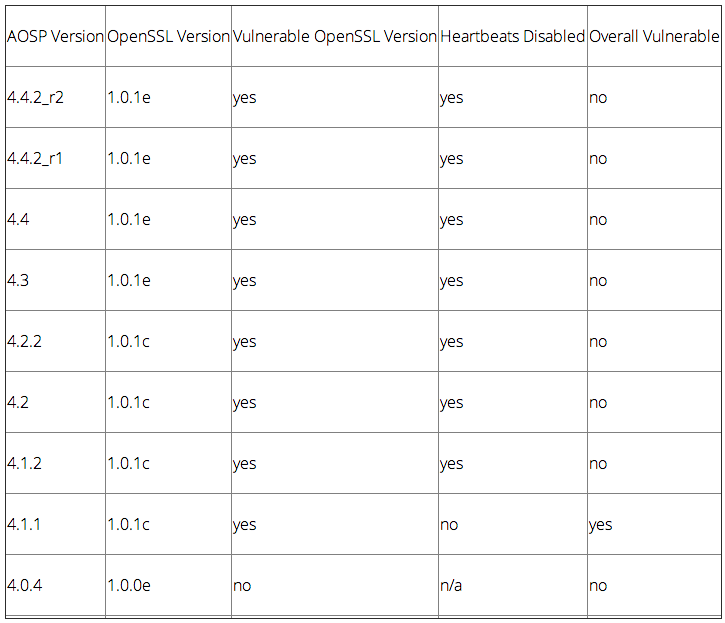
Bluebox, a security company, has done considerable work auditing Android versions from Ice Cream Sandwich and later (the OpenSSL bug that causes Heartbleed was only implemented after the release of Android 4.0, so Gingerbread and older are actually safe). They found that Android 4.1.1 is the only version inherently exposed to the SSL bug, as it implements both the insecure OpenSSL and heartbeats, which are disabled in subsequent releases.
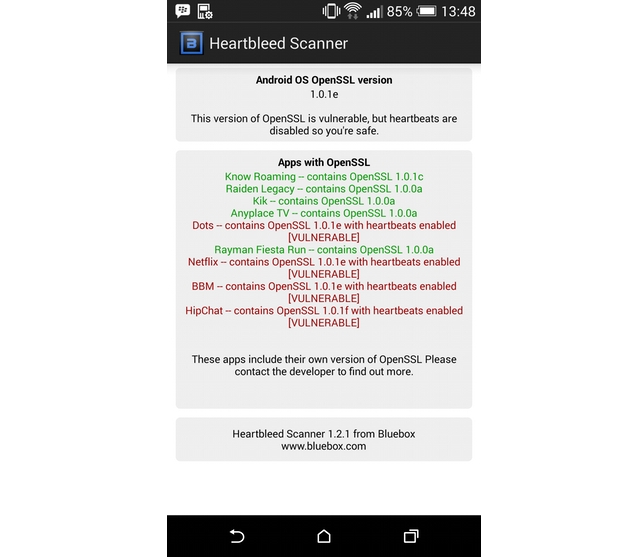
They’ve released a simple app called Heartbleed Scanner that looks through the OS itself and the apps installed therein to determine the ones still using older OpenSSL, as some developers integrate their own secure transport layer, while others use the one provided by Google. I was surprised to find that a number of my most-used messaging apps, including Kik, BBM and HipChat, are vulnerable.
All the companies listed above say that they’ve updated their certificates, and encourage users to change passwords just to be sure, but it’s alarming that a number of services were vulnerable for so long.
[source]Heartbleed Scanner[/source][via]Android Police[/via]
MobileSyrup may earn a commission from purchases made via our links, which helps fund the journalism we provide free on our website. These links do not influence our editorial content. Support us here.


